
Magento is a hugely popular platform, and with that level of success comes downsides. One of those downsides is that the platform attracts unwanted attention from those with malicious intent. Magento can (and does) store customer information, and merchant payment details - the impact of a breach can be huge on your business. Therefore, I have put together some tips towards hardening your site's security as part of my long standing experience as a Magento Solution Specialist and Magento partner.
The Magento Security Scan Tool is a 1 line script that can be added to your website, that enables you to regularly receive a report of security vulnerabilities such as malware and unauthorised access attempts. The tool is available in both the Commerce and Open Source versions. There are occasional false positives, but it’s a useful reassurance to have. We’ve written on this tool in more detail here.
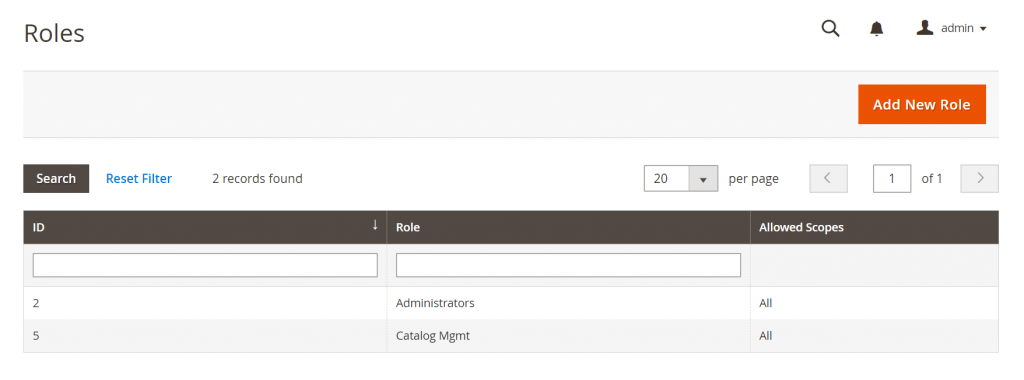
You’ll have a need for different people to access your site, and the bigger your team is, the more people will need access. Unfortunately, it’s really common for us to see all users given admin privileges. This means all these users for example can access and export customer details, and even edit payment details and prices. The list goes on and is simply an unnecessary amount of access for everyone on your team to have. We recommend that you restrict access based on who needs it applying the principle of “least privilege”. It makes sense and is just good IT housekeeping.
Then you really need to check who is being sent your site information. There are a number of alerts that can be sent out from Magento controlled by the admin panel, including error reports from Shopping feeds, failed payments and evening being bcc’d on sales emails. Often we find old developer or agencies' contact details hidden away and we’ve seen it before where customer details have been sent to these people even though you may have left the agency. Be sure to check what is being sent and to whom.
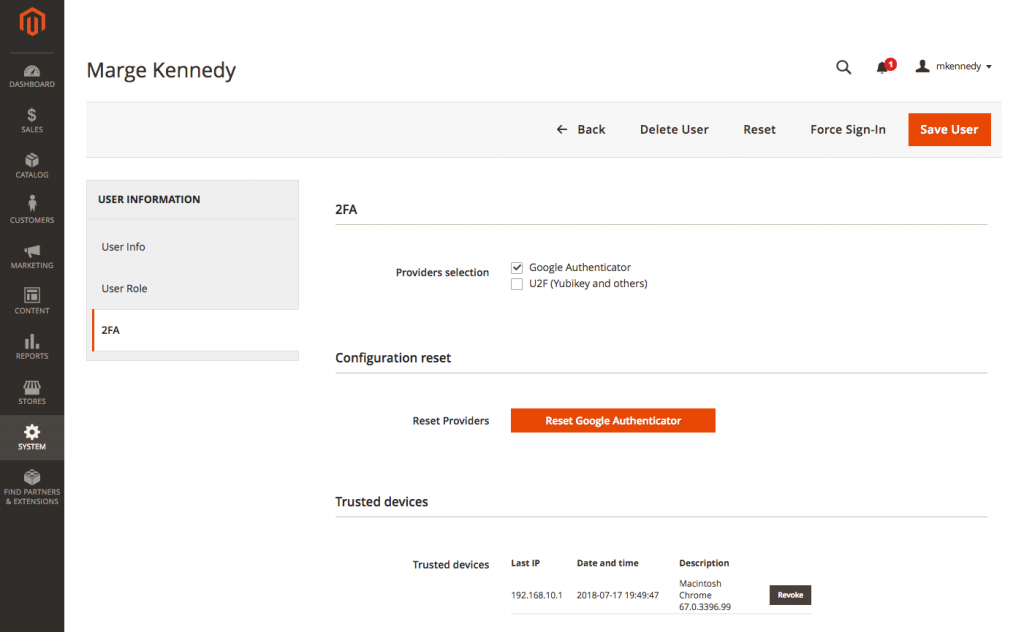
2FA (2 Factor Authentication) and ReCaptcha are now built into Magento as of 2.3 and are well known for restricting access and stopping malicious intent. There are a number of excellent authentication methods, but we often use Google's own authenticator which gives you a code from your mobile to input into Magento. We’ve written more on the subject here, including solutions for Magento 1.
A brute force attack is a trial-and-error method, usually by using automated software, to obtain information such as a user password. These kind of attacks should be picked up by your managed hosting provider, but one of the ways you can protect yourself and your site better is to ensure your admin URL isn’t the stock one provided to you by Magento. This ensures no-brute force attacks can happen as they won't know where the login form is to target.
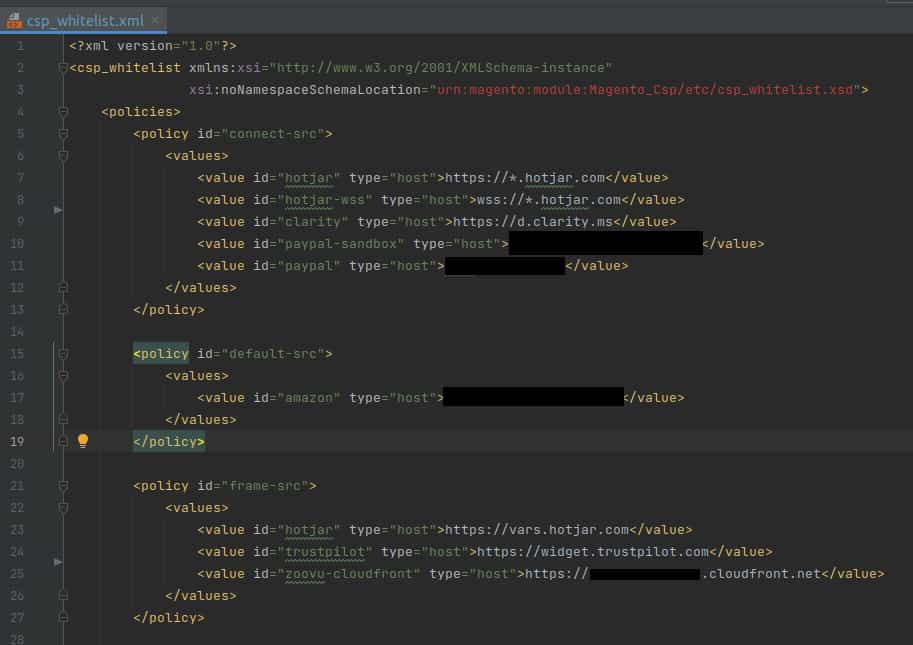
Magento 2.3.5 and Adobe Commerce can help keep your eCommerce website secure with its Content Security Policy. A CSP enables website owners to review any webpage URLs and content using its report mode. Trusted URLs can be whitelisted, whilst unwanted links can be blocked via the CSP's restrict mode. It's important to take a look at these with an experienced developer to enable that extra layer of security, preventing harmful content from loading such as malware.
Do ensure that your Magento eCommerce are patched and up to date – you’ll get bug fixes, features and security patches periodically. You can do this by checking in the footer of your admin panel against Magento’s releases (1.9.1 onwards). Alternatively, you can install the Magento Security Scan Tool – this will alert you to missing security patches. The releases are provided for a reason for Magento and shouldn’t be ignored.
At magic42, we take care of these kinds of security concerns for all our clients as part of our services a Magento development agency and Adobe Commerce development agency. Our Magento experts and Adobe Commerce partners can proactively help you manage your Magento site's security.
Iterative eCommerce Growth
Magento integrations
International eCommerce
To find out how we can help with your eCommerce website, please contact us.



